Are all Endpoint Securities the same?

When comparing endpoint security solutions, one thing quickly becomes clear: the messaging often sounds identical. Terms like “AI-driven,” “next-generation,” and “fully integrated” are used everywhere.
With most organizations now relying on endpoint protection instead of traditional antivirus, it’s easy to assume all tools deliver similar results.
That assumption doesn’t hold up.
As businesses grow and their security needs evolve—from basic prevention to advanced detection and response—the differences between solutions become much more apparent. What might initially seem like a simple feature comparison turns into a deeper architectural decision. The platform you choose today will shape not only your current security posture but also your ability to adapt and minimize risk as threats evolve.
So how do you cut through the marketing noise?
The importance of the underlying platform
A strong indicator of long-term value is the platform behind the solution. Not every feature will be necessary on day one—and that’s perfectly fine. What really matters is whether the foundation allows you to expand and strengthen your defenses over time.
This is where strategic thinking comes into play. Are you buying a product to solve an immediate need, or investing in a platform that can grow with your business?
Modern endpoint protection goes well beyond what’s installed on a device. It includes the data being collected, how systems integrate, the workflows it enables, and the infrastructure supporting it all. As artificial intelligence becomes more central to cybersecurity, the quality and scale of that underlying data become a major advantage.
It all comes down to data
AI systems are only as effective as the data they rely on. For automation and intelligent detection to work, the data must be accurate, diverse, and continuously updated. This aligns with four long-standing principles in data science: volume, variety, velocity, and veracity.
Applying these to endpoint security:
- Volume: How much data is being gathered? Does it reflect real-world attack activity at scale, including sophisticated techniques like hands-on-keyboard attacks and abuse of legitimate tools?
- Variety: Are insights limited to endpoints, or do they extend across email, networks, cloud environments, and identity systems? Broader data sources provide stronger context and visibility.
- Velocity: How quickly is new information processed and applied? Are threats incorporated into detection models in near real-time, or only after periodic updates?
- Veracity: How reliable is the data? Is it validated with threat intelligence and real-world incident response experience?
The quality of these elements ultimately determines how effectively a platform can identify and respond to emerging threats. Some solutions stay ahead of attackers, while others fall behind.
From prevention to full resilience
Endpoints are often the first line of defense—and one of the best opportunities to stop attacks early. However, a well-designed architecture allows you to extend protection across your entire environment, including email, networks, cloud services, and user identities.
From there, you can build comprehensive response capabilities that help contain incidents quickly and maintain business continuity even if something bypasses initial defenses.
Each layer you add strengthens your overall resilience. Detection speeds improve, response times shrink, and organizational risk decreases. And if managing this internally is a challenge, many businesses choose to work with providers offering around-the-clock managed detection and response (MDR) services that integrate directly with their platform.
Looking beyond the surface
When evaluating endpoint protection, it’s important to look past the marketing language. Ask deeper questions:
- What kind of data does the platform actually collect?
- How quickly does it learn from new threats?
- Who is validating and refining its intelligence?
The answers to these questions reveal far more than feature lists ever could.
In the end, effective cybersecurity is about more than just technology—it’s about building a sustainable strategy that protects operations, safeguards reputation, and supports long-term business success.
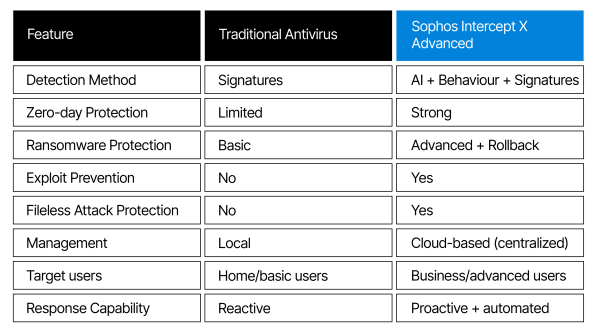
Antivirus vs Sophos Intercept X Advanced
Sophos Intercept X Advanced is next-generation endpoint protection. It protects computers and laptop (Windows & macOS) from ransomware, hacking attempts, malware and zero-day attacks, even ones that have never been used before. Think of it as antivirus++ (far more powerful than traditional antivirus).
Why Intercept X Advanced?
- Stops Malware and Viruses using AI
- Includes Crytoguard (ransomware defenses available)
- Anti-exploit Protection (Stops hacking techniques)
- Stops hackers after initial access (Active Adversary Protection)
- Automatic Cleanup & Root Cause Analysis